From when can we trace the origins of hacking and the existence of hackers in our
Par un écrivain mystérieux
Last updated 05 juillet 2024


What Is Hacking? Types of Hacking & More
Cyber insecurity: Hacking back

Hacker, Definition, Types, & Word Origin
How to know if your phone is hacked – Surfshark

Phone Hacking - How to Remove a Hacker
How to find out who hacked my website - Quora

How to Check If Website Has Been Hacked

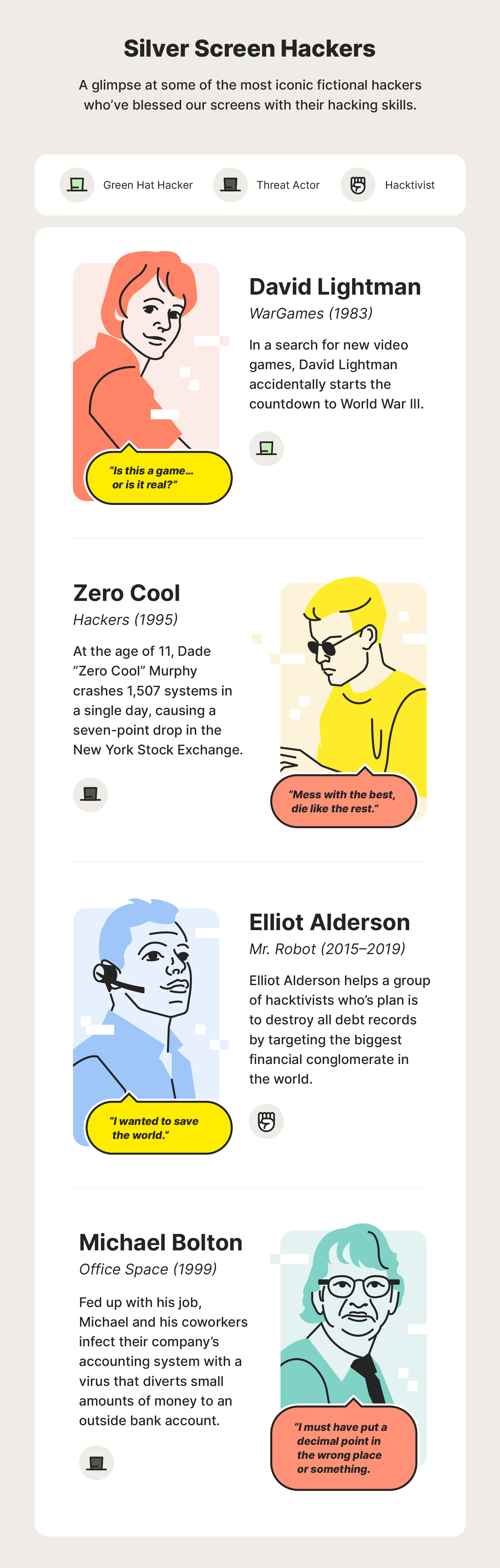
A Brief History of Hacking

How the US Lost to Hackers - The New York Times

Hacking the World – Part 3: The Hackers and the Hacked

What Are Hackers Thinking?

Leave no trace: how a teenage hacker lost himself online, Hacking
What is a hacker? + how to protect yourself - Norton
Recommandé pour vous
 What is Hacking?, Hacking Definition14 Jul 2023
What is Hacking?, Hacking Definition14 Jul 2023 The Evolution of Hacking14 Jul 2023
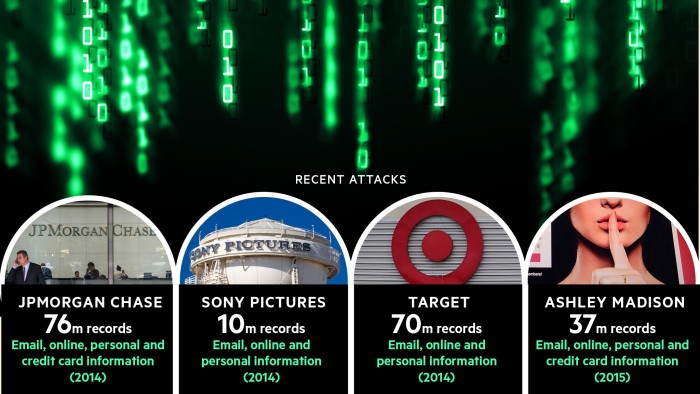
The Evolution of Hacking14 Jul 2023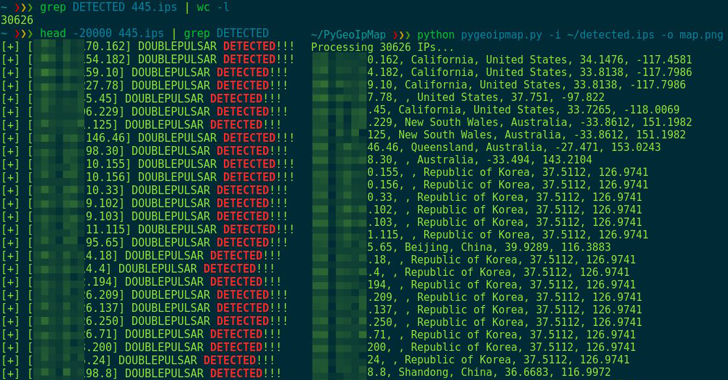 Leaked NSA Hacking Tools Being Used to Hack Thousands of Vulnerable Windows PCs14 Jul 2023
Leaked NSA Hacking Tools Being Used to Hack Thousands of Vulnerable Windows PCs14 Jul 2023 Potential hacking victims could be underprepared for threats from the shadows: Report - ABC News14 Jul 2023
Potential hacking victims could be underprepared for threats from the shadows: Report - ABC News14 Jul 2023 Prompt Hacking and Misuse of LLMs14 Jul 2023
Prompt Hacking and Misuse of LLMs14 Jul 2023 Ethical Hacking Course & Training14 Jul 2023
Ethical Hacking Course & Training14 Jul 2023 What Is Ethical Hacking?14 Jul 2023
What Is Ethical Hacking?14 Jul 2023 Is Ethical Hacking a Good Career?14 Jul 2023
Is Ethical Hacking a Good Career?14 Jul 2023- ETHICAL HACKING: THE NEW CYBER SECURITY FEATURE.14 Jul 2023
(1).pngL.jpg) Ethical Hacking Vs Perimeter Defense : Know the Difference14 Jul 2023
Ethical Hacking Vs Perimeter Defense : Know the Difference14 Jul 2023
Tu pourrais aussi aimer
 Peanut Butter Oreo Cookies - Kirbie's Cravings14 Jul 2023
Peanut Butter Oreo Cookies - Kirbie's Cravings14 Jul 2023 Whirlpool Réfrigérateur Frigo Combiné Inox 339l Froid Brassé Less Frost à Prix Carrefour14 Jul 2023
Whirlpool Réfrigérateur Frigo Combiné Inox 339l Froid Brassé Less Frost à Prix Carrefour14 Jul 2023- Pasquier - CONCOURS TERMINÉ Félicitations Mme Marie-france14 Jul 2023
 Feuille en silicone… - Cdiscount Jardin14 Jul 2023
Feuille en silicone… - Cdiscount Jardin14 Jul 2023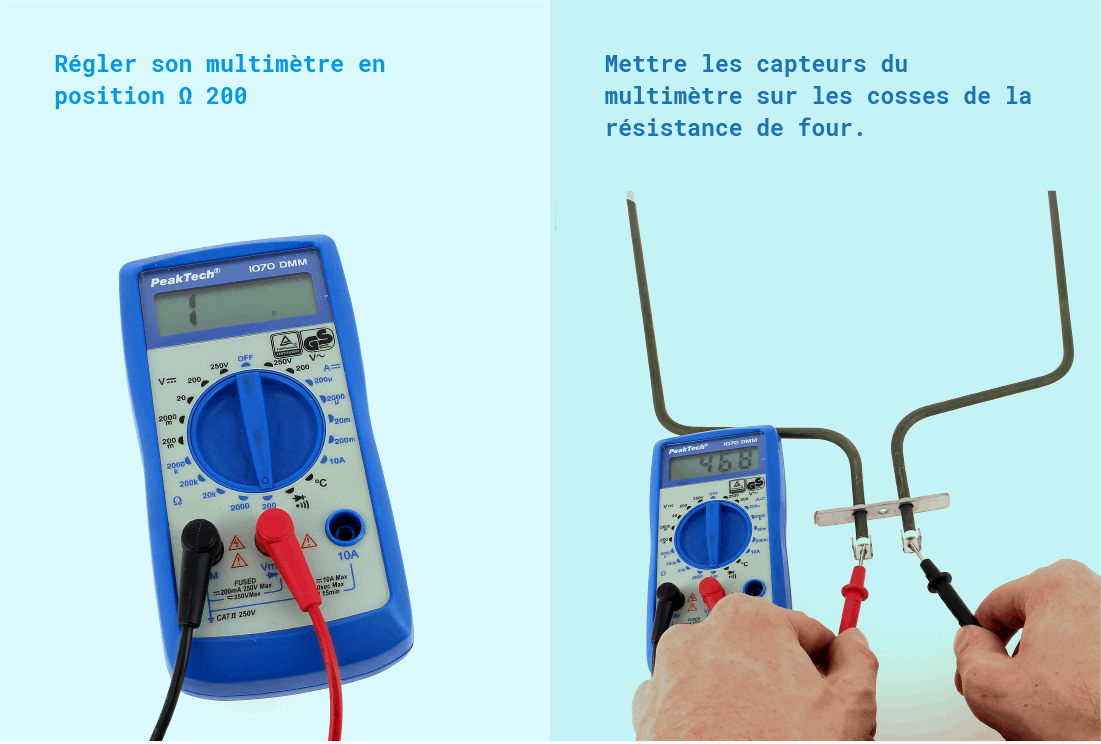 Comment bien utiliser un multimètre ?14 Jul 2023
Comment bien utiliser un multimètre ?14 Jul 2023 Figurine Manga One Piece Kaidou14 Jul 2023
Figurine Manga One Piece Kaidou14 Jul 2023 Samsung 980 Pro Heatsink Ssd M.2 Nvme Pcie 4.0 – Ps5 – 1 Terabyte – Avena Technologies14 Jul 2023
Samsung 980 Pro Heatsink Ssd M.2 Nvme Pcie 4.0 – Ps5 – 1 Terabyte – Avena Technologies14 Jul 2023 nouveau tout terrain amphibie réservoir quatre lecteur 8 canaux rc14 Jul 2023
nouveau tout terrain amphibie réservoir quatre lecteur 8 canaux rc14 Jul 2023 Fuseau de ski DUVILLARD Ingrid Long Noir Femme14 Jul 2023
Fuseau de ski DUVILLARD Ingrid Long Noir Femme14 Jul 2023 3 In 1 Board Games Tabletop Curling Bowling Game Shuffleboard14 Jul 2023
3 In 1 Board Games Tabletop Curling Bowling Game Shuffleboard14 Jul 2023

